How it Works
The Work Number® from Equifax automates the process of verifying your employees’ income and employment when they are purchasing or leasing a home or a car, renting an apartment, applying for a credit card, or requesting government benefits (such as SNAP) and more. Employees initiate the request themselves when they apply for credit or benefits through credentialed verifiers.
For example, one of your employees buys a car on the weekend and wants to finance through the dealer. They send the auto dealer to The Work Number website, where their employment and salary can be verified on the spot.
Our payroll software integrates with The Work Number to reduce your HR work and risks. Your employees benefit by improved opportunities for credit and government aid while also maintaining privacy. The employee will not have to provide pay stubs, as all the information is accessible 24/7 through the software integration between Equifax’s servers and our payroll servers. (PayPlus is not involved in this process at all. The transactions are confidential and happen “behind the scenes” through software.)
Automated Service
You can forget the paperwork. The Work Number service significantly lessens the manual verification workload.
When you respond to verification requests directly, your business might be at risk for fraud or error. The Work Number, as an automated verification, helps lessen risk over manual HR verification process.
Benefits to Employees
Faster and more informed decisions can improve opportunities for credit and aid.
More than 23% of all instant verifications completed through The Work Number service were completed after business hours or over the weekend.
Governed by the Fair Credit Reporting Act
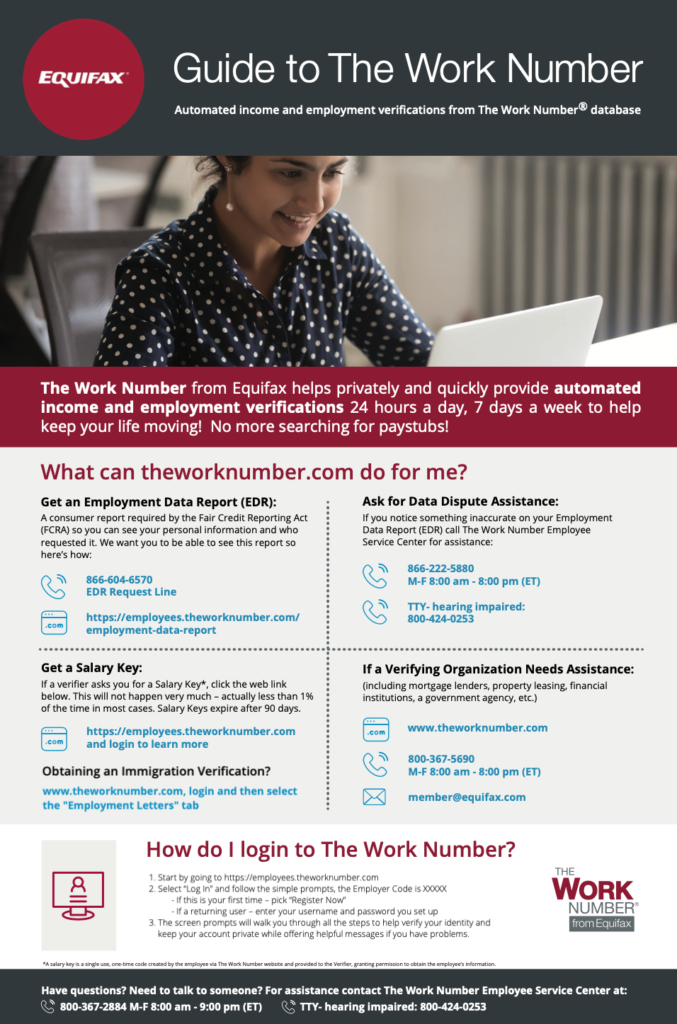
The Work Number is governed by the Fair Credit Reporting Act (FCRA), which helps ensure Verifiers have a valid reason to obtain employment information and employees can see who has requested their information and can dispute information that may be incorrect.
Privacy and Security
The Work Number uses stringent security standards to help protect employee information including data encryption, physical security controls, and user identity verification. Requests are initiated by employees, usually at the time of application, and only accepted from credentialed verifiers.


